What is Biometric Verification?
Every person has certain distinguishable traits that are unique only to them – be it their fingerprints, their face or even the pitch of their voice. These are our biometrics, and biometric verification uses these qualities to help identify people by that which makes them unique.
Let’s take a closer look at the most common forms of biometric verification, their features as well as limitations, before we go deeper into covering the benefits of biometric systems for customer onboarding and KYC processes.

What are the most common types of Biometric Verification?
Fingerprint recognition is likely the most common form of biometric verification that most people are familiar with, as it was a common feature on smartphones like the iPhone for many years. But even modern day digital assistants like Siri (and some phone-based services used in customer care) use someone’s voice to identify who is asking questions or making commands.
Regardless, biometrics give a higher level of assurance that someone is who they claim to be than a mere username or password ever could – which is why the business applications of biometric verification are so important. Biometrics can be used for everything from restricting access to certain files on a server to blocking access to certain portions of a building of a person does not expressly need to be there.
It’s a great way to make sure that your critical assets stay protected in the digital era, but it’s also a subset of technology that requires you to keep a few key things in mind.

What are the Limitations of Fingerprint Biometrics?
One of the most common types of biometrics available today involves fingerprint analysis – which, as the name suggests, uses a series of optical sensors to compare a live set of fingerprints with a recorded one, comparing how similar they are in a way that allows the system to verify someone’s identity.
While this technology is no doubt sophisticated, it also comes with its fair share of limitations. For starters, fingerprint biometrics are really only limited to smartphones for the time being. Very few laptops – and virtually no desktop computers – have fingerprint sensors installed inside them.
But more problematic is the fact that fingerprints can easily be spoofed – as was the case when the German politician Ursula von der Leyen (who is now the President of the European Commission!) had her fingerprints cloned by hackers using little more than photos taken with a camera phone.
Because fingerprint authentication relies on static information, it’s not difficult to bypass this level of security – potentially exposing an entire system’s worth of data to individuals with malicious intentions.

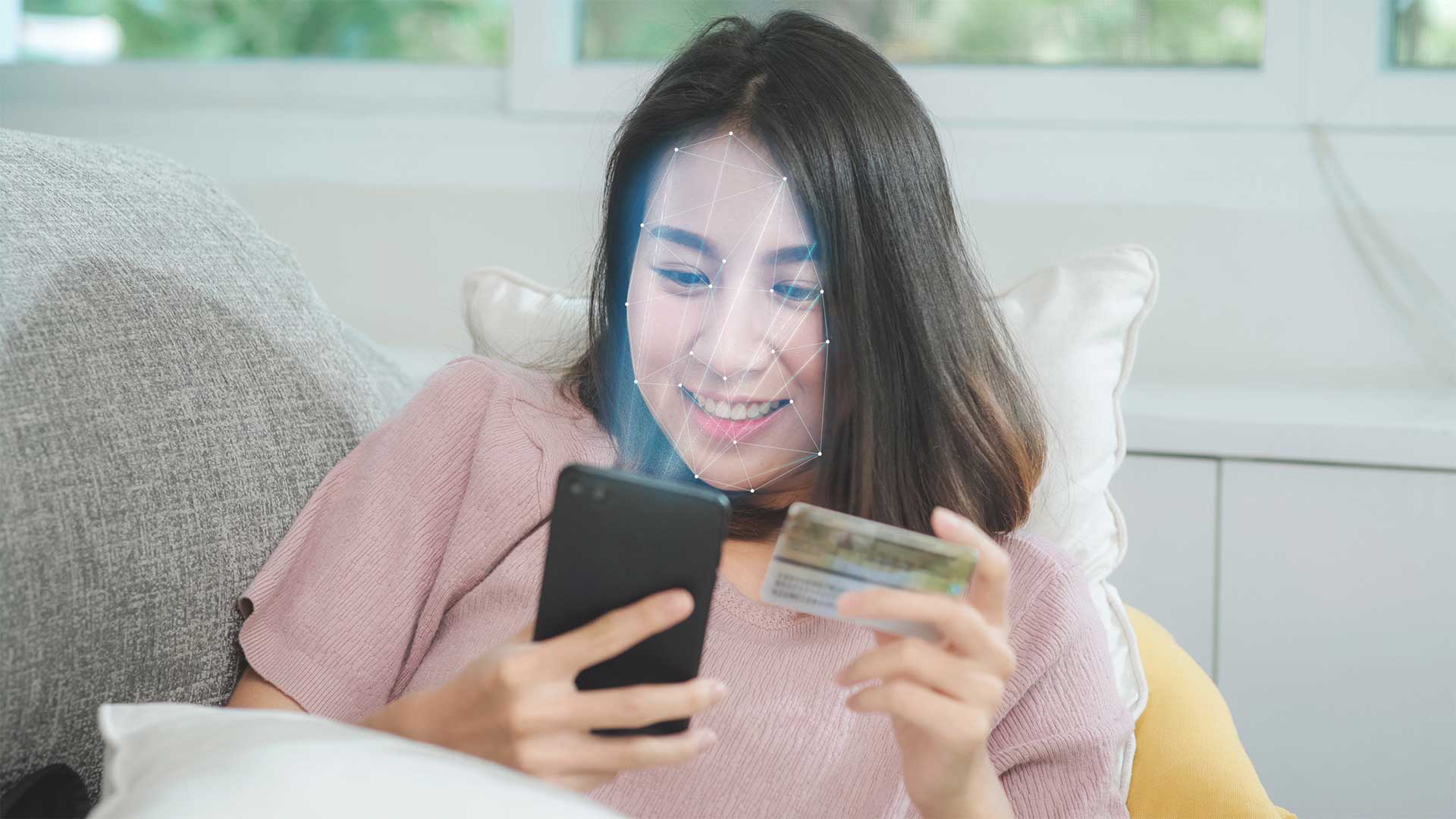
Face Authentication & Liveness Detection: The Most Effective Forms of Biometrics
Face authentication and liveness detection emerge as two of the best opportunities that businesses have to enjoy all the security-related benefits of biometric verification with as few of the potential downsides as possible.
This is because, unlike something like fingerprint biometrics alone, they provide a critical context to the authentication process that makes them far more accurate than alternatives.
First, the biometric solution identifies the “liveness” of the person in question – that is to say, it verifies that they are actually a living, breathing human being. At that point, it analyzes their image in three dimensions. This is how it “confirms” that it is look at a person, rather than a photo or some type of computer screen.
Finally, it authenticates their identity by comparing the face to some existing form of certified identification.
Secure Onboarding by Combining Biometric Systems
For the most secure mobile onboarding, these two technologies can be easily combined with ID scanning in a single verification process that takes under 10 seconds.
Aside from being fast, intuitive and easy to use, these seamless and secure processes unlock the most important benefit of all: the peace-of-mind that only comes with knowing that the security needs of your customers and your business are taken care of.